Network interfaces & requirements
Subnets
Our positioning servers have two independent network interfaces: The uplink network and the anchor network. Depending on when the server was bought, the port layout is different.
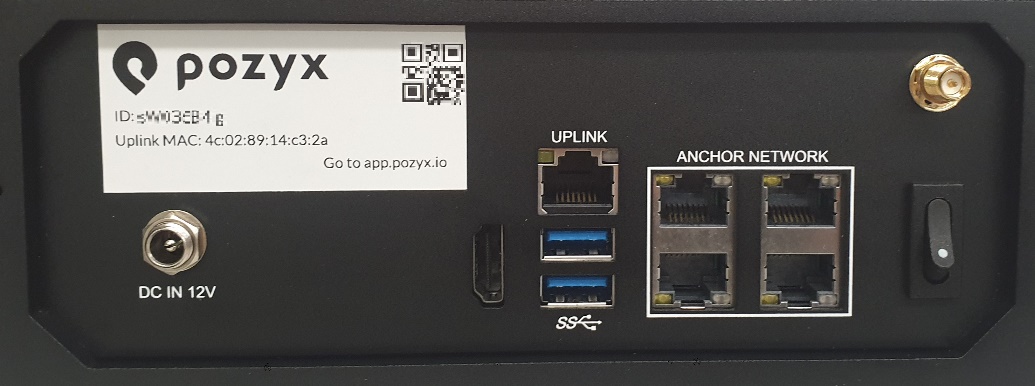
Here, the port for the uplink network is labeled LAN1 or UPLINK (depending on when you received your server), and the ports for the anchor network are labeled ANCHOR NETWORK.

Here, the port for the uplink network is labeled LAN1 and the ports for the anchor network are labeled LAN2 and LAN3.
If you would have a mini server having only two ports: LAN1 and LAN2. Then the port labeled LAN1 will be the uplink port and the LAN2 will be the anchor network port.
Uplink network
The uplink network is used to connect the positioning server to your home or company network. Through this port, the server is expected to reach the internet. By default the positioning server will request an IP address from the DHCP server running on this network, but it’s also possible to define a static IP address for the server.
Anchor network
The anchor network is used to connect the anchors to the positioning server. It is intended that only anchors (and network switches) are connected to this network. Also from a security point of view we recommend the anchor network to be isolated either physically or by using VLANs. On the anchor network of the positioning server, a DHCP server is configured which assigns IP addresses within the subnetwork 10.0.0.1/24. When a device is connected to the anchor network, it will receive an IP address from the positioning server, and it will be able to access the server through the static IP address 10.0.0.254.
Sometimes, it may occur that the subnet 10.0.0.1/24 is already in use for a different application. This is fine and will work if the anchor network is physically separated from the other network. Although if this is not the case and switches are shared for different applications, VLANs need to be configured on the switches. This will give problems if the subnet or any overlapping subnet is used in another part of the network. In these situations we can configure a different subnet on the positioning server for the anchor network, contact us through http://support.pozyx.io.
Network requirements
If you are using the Pozyx system from the cloud, make sure that the correct IP addresses and ports are whitelisted in your firewall. The Positioning server: Info page in the web application will highlight the required ports in green if they are accessible, or in red otherwise. A summary of the used ports and IP’s is given below:
Port 123 (NTP)
This port should be opened to all IP, unless a local NTP server is used. The NTP configuration of the positioning server can be changed in the Devices → Positioning server: Info page by clicking the “Edit NTP configuration” button.Port 53 (DNS)
This port should be opened for all IP in order to do domain name resolution, translating all the Pozyx FQDN’s and NTP domain names to an IP-address. A local DNS server can be used if this DNS server is advertised in the DHCP lease message from the DHCP server in the local network.Port 1194 (OpenVPN)
This port should only be opened for IP 34.247.139.22 in order for Pozyx engineers to give remote support. If this port is closed, the positioning system will still work but the possibility of remote support is limited.Port 443 (HTTPS and WSS)
This port has to be opened for 7 FQDN’s and their corresponding IP’s
There are 3 static IP addresses for the FQDN’s:
34.243.118.148
52.31.30.1
52.209.4.58
FQDN’scapi.cloud.pozyxlabs.com
uws.cloud.pozyxlabs.com
gws.cloud.pozyxlabs.com
uauth.cloud.pozyxlabs.com
gauth.cloud.pozyxlabs.com
ecr.cloud.pozyxlabs.com
ctdr.cloud.pozyxlabs.com
webhooks.cloud.pozyxlabs.com
The following URL also needs to be whitelisted for allowing remote updates of the software:
https://api.ecr.eu-west-1.amazonaws.com/
More information can be found here:
https://docs.aws.amazon.com/general/latest/gr/ecr.html
The ECR storing our container images uses an Amazon managed S3 bucket in the background. If this is not allowed or additional inspection is required, we can install your ZScaler root certificate on the device
Port number | Type | Direction | Purpose |
|---|---|---|---|
443 | TCP | OUT | HTTPS and WSS Required for usage of the Pozyx web application in the cloud and OpenVPN (the positioning server needs to authenticate itself to our cloud and request a VPN certificate before it can establish a VPN connection to our VPN server). |
123 | UDP | OUT | NTP Enables optional network system time synchronization. NTP is only needed for time synchronization with an already existing network. Internal synchronization of our RTLS (= synchronization of the clocks in the Pozyx anchors) does not require this. |
1194 | TCP/UDP1 | OUT | OpenVPN Required for remote support by Pozyx engineers. |
53 | TCP/UDP2 | OUT | DNS Required for usage of the Pozyx web application in the cloud and OpenVPN. |
1 https://openvpn.net/faq/why-does-openvpn-use-udp-and-tcp/
2 https://docs.microsoft.com/en-us/troubleshoot/windows-server/networking/dns-works-on-tcp-and-udp
